Exploring Surfshark’s Top Security Features: Double VPN, Kill Switch & More
Understanding Surfshark’s Approach to Modern Cybersecurity
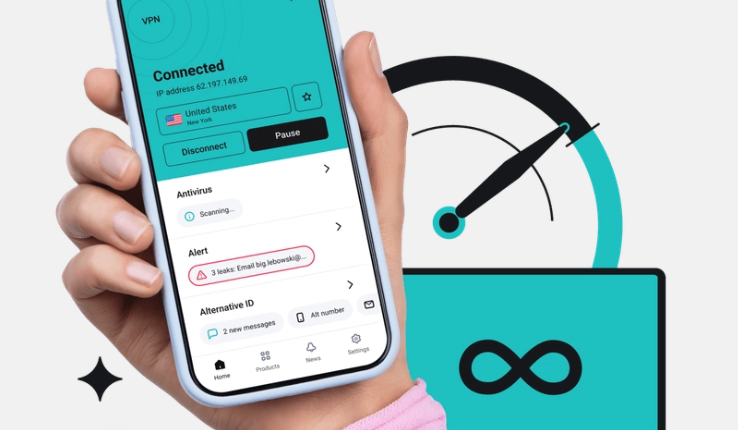
In a world where digital footprints are constantly tracked, analyzed, and monetized, online privacy has become more than just a technical concern; it is a fundamental necessity. Virtual private networks have evolved from niche tools used by technology enthusiasts into essential services for everyday users who value security, anonymity, and unrestricted internet access. Among the prominent providers in this space, Surfshark has carved out a strong reputation for delivering advanced security features while maintaining accessibility and ease of use. Exploring Surfshark’s top security features such as Double VPN, Kill Switch, and its broader privacy toolkit reveals how it addresses modern cyber threats and empowers users to take control of their online presence.
Surfshark was launched with the goal of making internet privacy accessible and affordable without compromising on advanced protection. Unlike many traditional VPN services that focus solely on IP masking, Surfshark integrates a comprehensive set of security mechanisms designed to tackle evolving digital risks. From data interception on public Wi-Fi networks to sophisticated tracking technologies employed by advertisers and cybercriminals, the online threat landscape is vast and continuously changing. Surfshark responds to these challenges with a layered security architecture that combines encryption, secure tunneling protocols, and specialized tools to reduce exposure at multiple levels.
At the core of Surfshark’s service lies strong encryption. It uses AES-256-GCM encryption, widely regarded as a gold standard in cybersecurity. This encryption method ensures that even if data is intercepted, it remains unreadable to unauthorized parties. Combined with secure tunneling protocols such as WireGuard, OpenVPN, and IKEv2/IPsec, Surfshark provides users with flexibility and performance without sacrificing security. WireGuard, in particular, is known for its speed and lightweight design, enabling faster connections while maintaining robust encryption standards.
Beyond encryption and protocols, Surfshark operates a strict no-logs policy. This means that it does not store records of users’ browsing activities, connection timestamps, session information, or IP addresses. For privacy-conscious individuals, this policy is critical because even the most advanced encryption would be undermined if a provider stored identifiable data. Surfshark’s privacy-focused jurisdiction and independent audits further reinforce user trust by demonstrating transparency in its operations.
Another foundational element of Surfshark’s approach is its global server network. By maintaining thousands of servers across numerous countries, Surfshark allows users to distribute their digital presence worldwide. This not only helps bypass geo-restrictions but also reduces server congestion and enhances performance. The ability to switch between servers easily adds another layer of anonymity, making it more difficult for third parties to correlate activities with a specific user.
While these core elements form the backbone of Surfshark’s security infrastructure, what truly differentiates it are the advanced features designed to mitigate specific vulnerabilities. Double VPN, Kill Switch, CleanWeb, MultiHop, Camouflage Mode, and NoBorders Mode each play a distinct role in fortifying online privacy. These features go beyond standard VPN functionality, addressing concerns such as traffic leaks, censorship, tracking, and advanced surveillance.
Surfshark’s commitment to user-friendly design also deserves attention. Security tools can often feel intimidating or overly technical, deterring average users from enabling important protections. Surfshark integrates its advanced features into intuitive applications across platforms including Windows, macOS, Android, iOS, and browser extensions. This accessibility ensures that users do not need extensive technical knowledge to benefit from enterprise-grade security mechanisms.
As cyber threats become more sophisticated, simply hiding an IP address is no longer sufficient. Data brokers aggregate browsing behaviors, malicious actors exploit unsecured networks, and certain regions impose heavy internet censorship. Surfshark’s comprehensive toolkit is built to confront these realities. By examining its standout features in depth, it becomes clear how each component contributes to a cohesive and resilient security ecosystem.
Double VPN and MultiHop: Layered Encryption for Maximum Anonymity
One of Surfshark’s most powerful and distinctive features is Double VPN, also known within its interface as MultiHop. This functionality routes internet traffic through two separate VPN servers instead of one, effectively adding an additional layer of encryption and obfuscation. While a standard VPN encrypts data and routes it through a single secure server, Double VPN takes this concept further by encrypting traffic twice and passing it through two different geographical locations.
The principle behind Double VPN is simple yet powerful. When a user activates MultiHop, their data is first encrypted on their device and sent to the first VPN server. At this point, the server decrypts the outer layer of encryption but immediately re-encrypts the traffic before forwarding it to the second server. Only after reaching the second server is the data sent to its final destination on the internet. This layered approach makes it significantly more difficult for anyone to trace the original source of the traffic.
From a privacy perspective, Double VPN enhances anonymity by separating knowledge of the user’s IP address from their final browsing activity. The first server knows the user’s real IP address but does not know the final destination of the traffic, while the second server sees the destination but not the original IP. This division of information reduces the risk of correlation and strengthens protection against advanced tracking or targeted surveillance.
Double VPN is particularly useful for individuals operating in high-risk environments. Journalists, activists, and users in heavily monitored regions may benefit from the additional layer of security when communicating sensitive information. Even for general users, enabling MultiHop can provide peace of mind when accessing financial accounts, conducting confidential research, or using public Wi-Fi networks.
However, this extra layer of encryption and routing can introduce a slight reduction in speed due to the increased distance and processing involved. Surfshark mitigates this impact through optimized server infrastructure and high-performance protocols such as WireGuard. Users can select from predefined MultiHop server pairs, strategically chosen to balance performance and security.
The flexibility offered by MultiHop allows users to tailor their privacy strategy. For example, one might route traffic through a server in Europe and then exit through North America, creating geographical dispersion that complicates tracking efforts. This feature transforms the VPN from a simple masking tool into a sophisticated privacy instrument capable of addressing more advanced threat models.
By implementing Double VPN in a user-friendly manner, Surfshark makes layered encryption accessible to everyday users. The feature can be activated with a single click within the application, eliminating the complexity traditionally associated with multi-layered network configurations. In doing so, Surfshark bridges the gap between high-level cybersecurity practices and consumer-friendly design.
Kill Switch and Leak Protection: Preventing Accidental Exposure
While encryption and multi-layer routing are crucial for security, even the strongest VPN can be undermined if the connection drops unexpectedly. This is where Surfshark’s Kill Switch becomes indispensable. The Kill Switch is designed to prevent accidental data exposure by automatically cutting off internet access if the VPN connection is interrupted.
Internet connections can fluctuate for various reasons, including unstable Wi-Fi, network congestion, or switching between networks. If a VPN disconnects during such transitions, a device may revert to its regular internet connection, exposing the user’s real IP address and unencrypted traffic. The Kill Switch eliminates this vulnerability by immediately blocking all outgoing internet traffic until the secure VPN connection is restored.
This feature is particularly important for users engaged in activities where privacy is critical. Whether accessing sensitive work documents, handling financial transactions, or communicating privately, even a brief exposure could compromise confidentiality. The Kill Switch ensures continuity of protection, acting as a safeguard against unexpected disconnections.
Surfshark’s Kill Switch operates seamlessly in the background, requiring minimal user intervention once enabled. Users can choose to activate it permanently or only during specific sessions, depending on their needs. The application provides clear notifications if the Kill Switch is triggered, allowing users to understand why their internet access may be temporarily paused.
Beyond the Kill Switch, Surfshark incorporates comprehensive leak protection mechanisms. DNS leaks, IPv6 leaks, and WebRTC leaks can reveal identifying information even when a VPN is active. Surfshark addresses these risks by routing DNS requests through its secure servers and disabling IPv6 traffic when necessary. WebRTC leak protection ensures that browser-based communications do not bypass the encrypted tunnel.
Together, the Kill Switch and leak protection systems create a robust safety net. They address one of the most overlooked aspects of VPN usage: the potential for technical glitches to undermine security. By proactively preventing data exposure rather than merely encrypting traffic, Surfshark demonstrates a holistic approach to privacy.
In environments where network stability is uncertain, such as airports, hotels, and cafes, these features are invaluable. Public Wi-Fi networks are notoriously insecure, often lacking proper encryption and susceptible to man-in-the-middle attacks. With Surfshark’s safeguards in place, users can connect to such networks with significantly reduced risk.
Ultimately, the Kill Switch is not just a secondary feature; it is a critical component of reliable VPN protection. By ensuring that privacy is maintained even during technical disruptions, Surfshark reinforces its commitment to continuous and uncompromised security.
CleanWeb, Camouflage Mode, and NoBorders: Advanced Protection Against Tracking and Censorship
Modern online threats extend beyond hackers intercepting data. Advertisers track browsing behavior, malicious websites distribute malware, and certain governments enforce internet censorship. Surfshark addresses these challenges with features designed to enhance both security and accessibility, including CleanWeb, Camouflage Mode, and NoBorders Mode.
CleanWeb functions as an integrated ad blocker and malware filter. It prevents intrusive advertisements, blocks trackers, and restricts access to known malicious domains. By filtering harmful content at the DNS level, CleanWeb reduces the risk of phishing attacks and drive-by downloads. It also improves browsing speed and user experience by eliminating resource-heavy advertisements.
Tracking scripts embedded in websites collect detailed data about user behavior, from pages visited to time spent on specific content. CleanWeb disrupts these tracking mechanisms, limiting the data that advertisers and analytics companies can gather. This not only enhances privacy but also reduces digital profiling.
Camouflage Mode adds another layer of stealth by making VPN traffic appear as regular internet traffic. In some regions or networks, VPN usage itself may be monitored or restricted. Deep packet inspection techniques can identify VPN protocols and block connections. Camouflage Mode disguises encrypted traffic, making it difficult for network administrators or authorities to detect VPN usage.
This feature is particularly relevant in countries with strict internet regulations. By masking VPN signatures, Surfshark enables users to maintain access to open internet resources without drawing attention to their connection methods. It ensures that the act of protecting one’s privacy does not itself become a vulnerability.
NoBorders Mode complements Camouflage Mode by automatically detecting network restrictions and providing a list of optimized servers for challenging environments. When Surfshark senses restrictive conditions, it adjusts server availability to ensure stable connectivity. This dynamic response enhances reliability in regions where VPN connections may otherwise be unstable or blocked.
Together, these features position Surfshark as more than a basic privacy tool. They transform it into a comprehensive solution for navigating a complex digital landscape marked by surveillance, advertising ecosystems, and censorship barriers. By integrating ad blocking, traffic obfuscation, and adaptive connectivity, Surfshark addresses threats that extend beyond traditional hacking.
The combination of CleanWeb, Camouflage Mode, and NoBorders Mode illustrates Surfshark’s understanding of real-world usage scenarios. Privacy today is not just about encryption; it is about controlling data exposure, avoiding tracking, and maintaining unrestricted access to information. Surfshark’s advanced protections reflect this broader vision of digital freedom.
Additional Security Tools and the Future of Online Privacy with Surfshark
Beyond its headline features, Surfshark offers several additional tools that strengthen its security ecosystem. One notable feature is split tunneling, which allows users to choose which applications or websites route through the VPN and which connect directly to the internet. This flexibility is particularly useful for balancing security and performance, enabling users to protect sensitive activities while maintaining direct access to local services.
Surfshark also provides private DNS on each server, ensuring that DNS queries remain encrypted within the VPN tunnel. This prevents internet service providers from monitoring domain requests and enhances overall confidentiality. The use of RAM-only servers further reinforces privacy, as data stored on volatile memory is automatically wiped upon reboot, reducing the risk of long-term data retention.
Another important aspect is unlimited simultaneous connections. Unlike many competitors that restrict the number of devices per subscription, Surfshark allows users to protect all their devices under a single account. This encourages comprehensive security coverage across smartphones, laptops, tablets, and even smart TVs.
Surfshark’s commitment to transparency is demonstrated through independent security audits conducted by reputable cybersecurity firms. These audits assess the integrity of its infrastructure and verify claims such as its no-logs policy. By inviting third-party scrutiny, Surfshark strengthens user confidence and sets a standard for accountability within the VPN industry.
Looking ahead, the future of online privacy will likely involve even more sophisticated tracking technologies and cyber threats. Artificial intelligence-driven surveillance, advanced fingerprinting techniques, and evolving malware strains will challenge traditional security models. In response, VPN providers must continue innovating to stay ahead of these developments.
Surfshark appears well-positioned to adapt to this evolving landscape. Its emphasis on layered security, user-friendly design, and proactive threat mitigation demonstrates a forward-thinking philosophy. Features such as Double VPN, Kill Switch, CleanWeb, Camouflage Mode, and NoBorders Mode are not isolated tools but components of a comprehensive strategy aimed at preserving digital autonomy.
As users become more aware of the value of their personal data, demand for robust privacy solutions will continue to grow. Surfshark’s blend of advanced security features and accessible design makes it appealing to both novices and experienced users. By combining strong encryption, traffic obfuscation, ad blocking, leak protection, and multi-layer routing, it provides a versatile defense against modern cyber risks.
In conclusion, exploring Surfshark’s top security features reveals a service built on the principles of resilience, adaptability, and user empowerment. Double VPN enhances anonymity through layered encryption, the Kill Switch safeguards against accidental exposure, and additional tools address tracking, censorship, and malware threats. Together, these elements form a cohesive and comprehensive security framework designed to meet the challenges of today’s interconnected world.